Browser-in-the-Browser (BITB) attacks are becoming more and more common. These attackers are looking for account credentials. The attack consists of a hacker writing JavaScript code to present a “pop-up” window that is another phishing disguise to lure unsuspecting users into typing their account credentials, which are then sent to the hacker. These pop-up windows are very difficult to discern if they are real or fake.
BITB attacks take advantage of third party single sign-on (SSO) options to offer the spoofed pop-up window. What makes the attack so difficult to tell if it’s fake is that in addition to the pop-up window, a URL is shown that may look legitimate. See the example below.
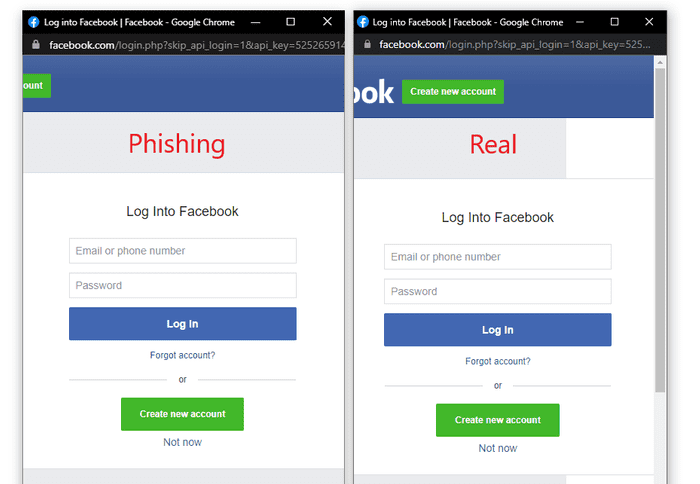
Image credit: mr.d0x
Most people are so used to seeing these type of pop-up windows, they don’t really question it. Users typically get tricked into visiting the malicious page through a phishing email or instant messaging software.
What Can Be Done?
Unfortunately these attacks won’t lessen up and attackers will continue to find ways to trick users. Below are a few things that business can do:
- Implement strict user account permissions
- Use password managers since the phishing page is fake, the autocomplete option of the password manager might not react to it
- Do not click on links or attached files coming from unknown sources via email or instant messaging software – ask your IT department if you’re not sure
- Install antivirus software on devices
- Use a firewall
- Keep software programs up to date
- Do regular backups
- Develop a cyber security policy and provide training that includes phishing techniques, social engineering and how to detect a compromised computer or device
Bottom line, browser-in-the-browser attacks are difficult to detect and to defend against, but they are easy to prevent. Practicing safe browsing and email habits will prevent such an attack in most cases.
If you are a business and use email and the internet to conduct business, you are at risk of a browser-in-the-browser attack. As your telecom and IT solutions expert, REACH takes pride in keeping you connected and protected. We can help you with a cyber security risk assessment, develop a cyber security strategy and provide cyber security solutions to help keep your data safe. Connect with us today by calling Valerie at 715-330-4200 or filling out our contact form.
